If you’ve ever stumbled across the strange-looking string content://cz.mobilesoft.appblock.fileprovider/cache/blank.html explained in your phone logs or browser history, yeah—it definitely looks suspicious at first glance. It kinda feels like a broken link or even something shady. But honestly, it’s neither.
What you’re seeing is a completely normal part of how the Android operating system handles secure file access and blocks content through apps like AppBlock. Once you understand what’s going on behind the scenes, it actually becomes pretty simple… even if it looks technical.
Let’s break it down properly.
What Does content://cz.mobilesoft.appblock.fileprovider/cache/blank.html Mean?
Short answer: It’s a Content URI used by Android to securely load a blank placeholder page when content is blocked.
Now the slightly longer, but still simple version.
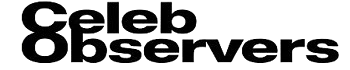
This string is made of three key parts:
| Component | Meaning |
|---|---|
| content:// | Indicates a Content URI, not a web URL |
| cz.mobilesoft.appblock.fileprovider | The authority (AppBlock’s file-sharing component) |
| /cache/blank.html | A file stored in the app’s cache directory |
So basically:
Content URI → points to → a local blank HTML file inside AppBlock
This is not a broken link. It’s more like an internal shortcut Android uses to load safe, controlled content.
Understanding Content URIs in Android (The Core Concept)
Let’s simplify this because it sounds more complicated than it is.
What is a Content URI?
A Content URI is a secure identifier that allows apps to share files without exposing actual file paths.
Content URI → enables → secure file sharing between Android apps
Instead of showing raw paths like:
/data/data/app/files/example.html
Android uses:
content://something/safe
This protects your data. Pretty smart system tbh.
Why Not Use Normal File Paths?
Because Android enforces sandboxing, meaning:
- Apps cannot access each other’s private data directly
- Internal storage stays hidden
- Permissions control everything
So yeah, Content URIs are basically a safety layer.
Read Articul: https://celebobservers.com/content-cz-mobilesoft-appblock-fileprovider-cache-blank-html-explained/
How AppBlock Uses This System
The app behind this string is AppBlock, a tool designed to block distracting apps and websites.
What Happens When a Site Gets Blocked?
Here’s the simple flow:
- You try to open a blocked website
- AppBlock intercepts the request
- Instead of loading the site, it loads a local file
- That file is blank.html
So:
AppBlock → uses → FileProvider to serve blocked content placeholder
This placeholder is either:
- Completely blank
- Or shows a simple “blocked” message
And that’s why you see the content URI.
Why a Blank HTML File (blank.html)?
Good question, and yeah it seems odd at first.
Reasons AppBlock Uses blank.html
- Speed: Local files load instantly
- No errors: Avoids messy browser error pages
- Clean UX: Keeps things simple and distraction-free
- Privacy: No external requests are made
So:
Blank HTML file → replaces → blocked website content
It’s basically a clean “nothing here” page.
Inside FileProvider: The Hidden Gatekeeper
Now we get slightly technical, but I’ll keep it human.
What is FileProvider?
FileProvider is an Android component that lets apps share files securely.
FileProvider → restricts → access to specific app directories via permissions
Instead of exposing everything, it only allows access to:
- Specific folders (like
/cache/) - Specific file types
- Temporary access only
How It Works (Simplified)
- Defined in the app’s Android manifest
- Uses XML to define allowed paths
- Grants temporary permissions when needed
So yeah, it’s basically a controlled gateway, not an open door.
How Android Actually Loads This File
This part is kinda cool if you think about it.
Behind-the-Scenes Process
- App requests a Content URI
- Android checks permissions
- Content Resolver steps in
- File is opened securely
So:
Content Resolver → retrieves → data from content URIs securely
No direct file access ever happens.
Where You Might See This URI in Real Life
You’re not crazy—this string can appear in a few places.
Common Scenarios
- Browser history → when a blocked page is replaced
- WebView apps → when content is intercepted
- Developer logs → during debugging
- System reports → tracking resource access
And yeah, it always looks confusing the first time.
Is content://cz.mobilesoft.appblock.fileprovider/cache/blank.html Safe?
Short answer: Yes, 100% safe.
It is:
- Not malware
- Not a phishing link
- Not tracking you
It’s just:
Android security system → protects → internal app data
Honestly, if you see this, it means your system is working properly.
How to Stop Seeing This (If It Annoys You)
If you’re tired of seeing it, here’s what you can do.
Option 1: Adjust AppBlock Settings
- Open AppBlock
- Go to Web Blocking
- Remove certain websites
Option 2: Pause AppBlock
- Use quick settings toggle
- Temporarily disable blocking
Option 3: Clear Cache
- Settings → Apps → AppBlock → Storage
- Tap Clear Cache
Option 4: Uninstall AppBlock
- Completely removes the behavior
Simple fixes, nothing complicated.
Deep Dive: Why Android Uses Content Providers
Let’s zoom out a bit.
Benefits of Content Providers
- No raw file exposure
- Fine-grained permissions
- Temporary access control
- Secure inter-app communication
So:
Content Provider → ensures → safe cross-app data sharing
It’s one of Android’s biggest security features honestly.
Topical Gap 1: Can Content URIs Be Exploited? (Security Perspective)
Most articles skip this, but it matters.
Potential Risks (Rare but Real)
If badly configured:
- Apps could expose sensitive files
- Weak permissions might allow misuse
- Developers might accidentally over-share
Best Practices to Stay Safe
- Use trusted apps only
- Keep apps updated
- Avoid unknown APK installs
But in this case, AppBlock is safe and widely used.
Topical Gap 2: Developer Implementation (Real Insight)
Let’s make this useful for devs too.
Basic Code Example
InputStream input = getContentResolver().openInputStream(uri);
WebView Interception
shouldInterceptRequest(WebView view, WebResourceRequest request)
Key Tips
- Always check permissions
- Use correct MIME types (
text/html) - Avoid hardcoding file paths
This is where many devs mess up, honestly.
Best Practices for Handling Content URIs
If you’re building apps, keep this in mind:
- Use unique authority names
- Limit shared directories
- Grant temporary permissions only
- Avoid logging sensitive URIs
- Keep files lightweight
These small things make a big difference.
Final Thoughts
At first glance, content://cz.mobilesoft.appblock.fileprovider/cache/blank.html looks confusing, maybe even worrying. But really, it’s just Android doing its job.
It represents:
- Secure file sharing
- Smart content blocking
- Clean placeholder handling
Once you get it, it’s actually pretty logical… just not very user-friendly looking.
Frequently asked questions
1. Is content://cz.mobilesoft.appblock.fileprovider/cache/blank.html harmful?
No, it’s completely safe. It’s just a local Content URI used by AppBlock to show a placeholder page instead of blocked content. It doesn’t harm your device or access sensitive data.
2. Why does this appear in my browser history?
When AppBlock blocks a website, it loads a local blank HTML file instead. Your browser records that as a visited page, which is why the Content URI shows up in history.
3. Can I open this link normally?
Not really. Content URIs require permission and must be accessed through Android’s Content Resolver. Regular browsers don’t fully understand or handle them directly.
4. Does this mean my phone is infected?
No, not at all. This is a normal Android system behavior tied to app functionality. It has nothing to do with viruses or malware.